Protect Against Port Spoofing in the Cloud
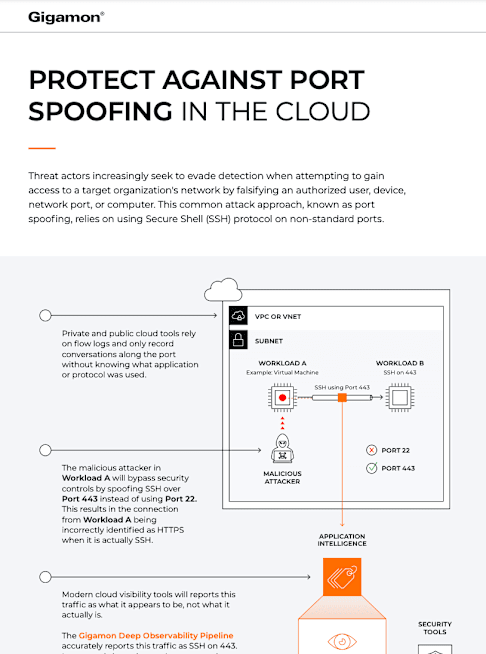
Threat actors increasingly seek to evade detection when attempting to gain access to a target organization's network by falsifying an authorized user, device, network port, or computer. This common attack approach, known as port spoofing, relies on using Secure Shell (SSH) protocol on non-standard ports.